The leads4pass 300-720 dumps have been updated to include 94 questions and answers for your Securing Email with Cisco Email Security Appliance, SESA exam prep.
Therefore, you can come to leads4pass to choose the latest 300-720 dumps to practice all 300-720 dumps questions and answers before taking the actual Securing Email with Cisco Email Security Appliance (SESA) exam.
We guarantee that the leads4pass 300-720 Dumps is the best option to help you successfully pass the actual Cisco 300-720 exam.
Cisco 300-720 Exam Details:
Vendor: Cisco
Exam Code: 300-720
Exam Name: Securing Email with Cisco Email Security Appliance (SESA)
Certification: CCNP
Duration: 90 minutes
Languages: English
Price: $300 USD
Number of Questions: 55-65
Passing score: Variable (750-850 / 1000 Approx.)
300-720 dumps 2022: https://www.leads4pass.com/300-720.html
[Free Q1-Q13] Cisco 300-720 Dumps Exam Questions and Answers:
QUESTION 1:
An engineer is configuring an SMTP authentication profile on a Cisco ESA which requires certificate verification. Which
the section must be configured to accomplish this goal?
A. Mail Flow Policies
B. Sending Profiles
C. Outgoing Mail Policies
D. Verification Profiles
Correct Answer: A
QUESTION 2:
Which SMTP extension does Cisco ESA support for email security?
A. EARN
B. UTF8SMTP
C. PIPELINING
D. STARTTLS
Correct Answer: D
QUESTION 3:
Which two certificate authority lists are available in Cisco ESA? (Choose two.)
A. default
B. system
C. user
D. custom
E. demo
Correct Answer: BD
QUESTION 4:
Which two features of Cisco Email Security are added to a Sender Group to protect an organization against email
threats? (Choose two.)
A. NetFlow
B. geolocation-based filtering
C. heuristic-based filtering
D. senderbase reputation filtering
E. content disarm and reconstruction
Correct Answer: CD
QUESTION 5:
Which two Cisco ESA features are used to control email delivery based on the sender? (Choose two.)
A. incoming mail policies
B. spam quarantine
C. outbreak filter
D. safelists
E. blocklists
Correct Answer: DE
QUESTION 6:
Which feature utilizes sensor information obtained from Talos intelligence to filter email servers connecting into the
Cisco ESA?
A. SenderBase Reputation Filtering
B. Connection Reputation Filtering
C. Talos Reputation Filtering
D. SpamCop Reputation Filtering
Correct Answer: A
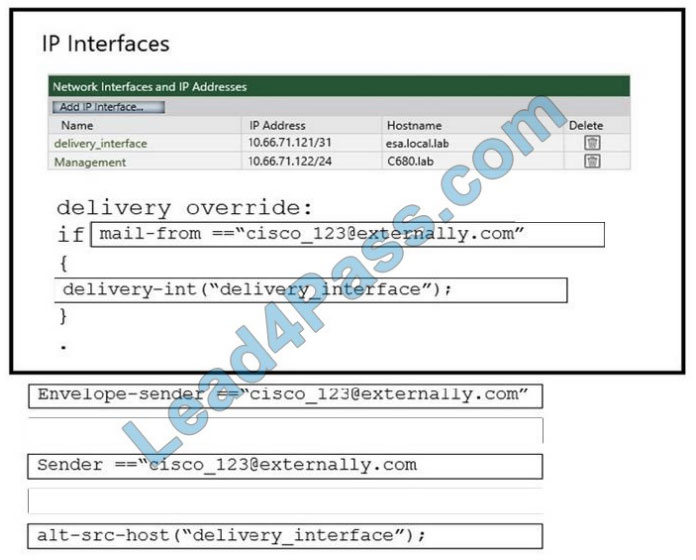
QUESTION 7:
DRAG-DROP
An administrator must ensure that emails sent from [email protected] are routed through an alternate virtual
gateway. Drag and drop the snippet from the bottom onto the blank in the graphic to finish the message filter syntax. Not
all snippets are used.
Select and Place:
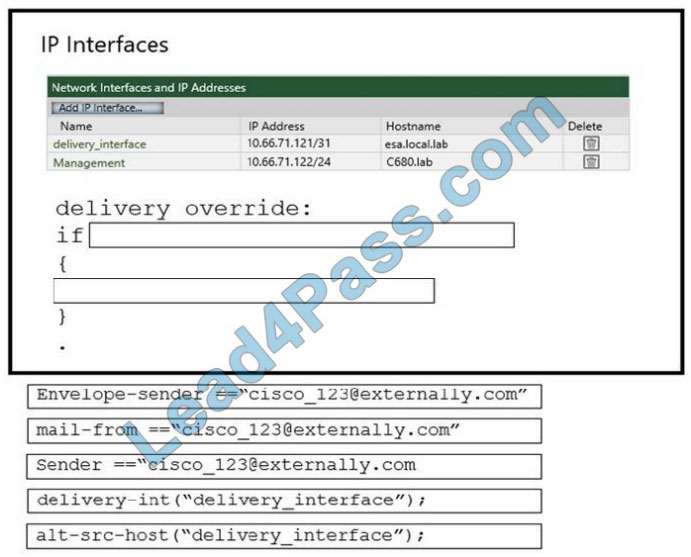
Correct Answer:
QUESTION 8:
Refer to the exhibit.
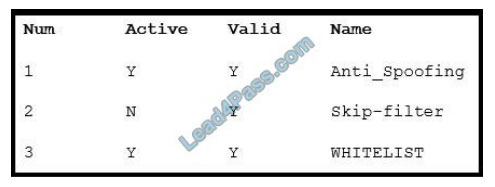
What is the correct order of commands to set filter 2 to active?
A. filters-> edit-> 2-> Active
B. filters-> modify-> All-> Active
C. filters-> detail-> 2-> 1
D. filters-> set-> 2-> 1
Correct Answer: D
QUESTION 9:
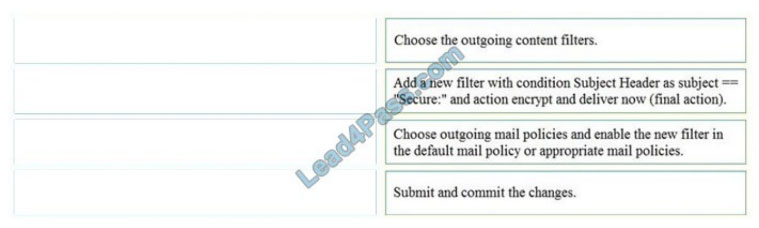
DRAG-DROP
An Encryption Profile has been set up on the Cisco ESA.
Drag and drop the steps from the left for creating an outgoing content filter to encrypt emails that contain the subject
“Secure:” into the correct order on the right.
Select and Place:
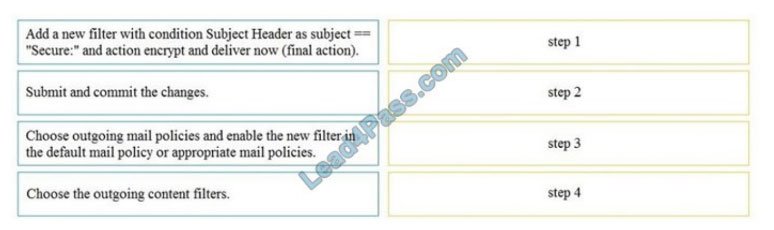
Correct Answer:
QUESTION 10:
When the Cisco ESA is configured to perform antivirus scanning, what is the default timeout value?
A. 30 seconds
B. 90 seconds
C. 60 seconds
D. 120 seconds
Correct Answer: C
QUESTION 11:
Spreadsheets containing credit card numbers are being allowed to bypass the Cisco ESA.
Which outgoing mail policy feature should be configured to catch this content before it leaves the network?
A. file reputation filtering
B. outbreak filtering
C. data loss prevention
D. file analysis
Correct Answer: B
QUESTION 12:
How does the graymail safe unsubscribe feature function?
A. It strips the malicious content of the URI before unsubscribing.
B. It checks the URI reputation and category and allows the content filter to take any action on it.
C. It redirects the end-user who clicks the unsubscribe button to a sandbox environment to allow a safe unsubscribe.
D. It checks the reputation of the URI and performs the unsubscribe process on behalf of the end-user.
Correct Answer: D
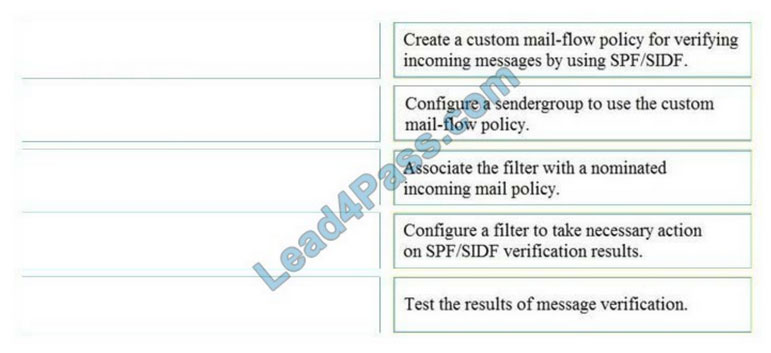
QUESTION 13:
DRAG-DROP
Drag and drop the steps to configure Cisco ESA to use SPF/SIDF verification from the left into the correct order on the
right.
Select and Place:
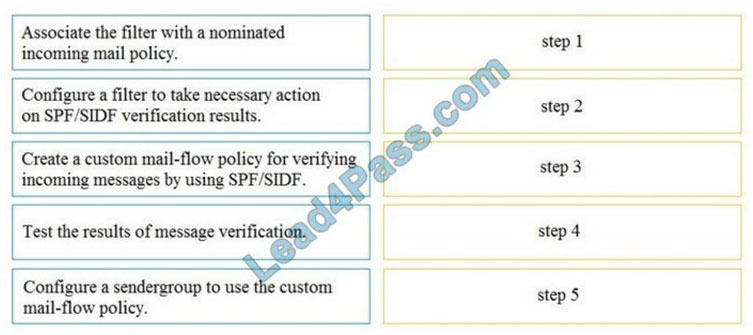
Correct Answer:
……
[Free Q1-Q13] Cisco 300-72 Dumps 0 Exam Questions and Answers online download: https://drive.google.com/file/d/1iGRGN8GVZcVPdS2PKRslf9_nBqBWlkM_/
Get more 300-720 dumps questions and answers: Click here

Recent Comments